Cybercriminals Leverage Microsoft Copilot for Sophisticated Phishing Strategies
Microsoft Copilot Under Attack: The Rise of Phishing Scams
Overview of Microsoft Copilot
Microsoft Copilot is a Generative AI assistant that has been introduced to streamline tasks for users within Microsoft’s suite of applications, such as Word and Outlook. Much like OpenAI’s ChatGPT, it aids in various functions, including drafting emails and generating documents. However, its recent rollout has created a new avenue for cybercriminals, making users susceptible to advanced phishing attacks.
The Phishing Threat
Hackers are exploiting Microsoft Copilot’s novelty to launch sophisticated phishing campaigns. According to a report by Cofense, employees may not fully understand how to use Copilot, which increases their chances of falling victim to these scams. Here are some methods utilized in these phishing attempts:
1. Invoice Spoofing
- Tactic: Fraudulent emails are sent that appear to originate from the "Co-pilot." These emails often contain phony invoices for services that were never requested.
- Risk: Due to the newness of the Copilot feature, employees may be uncertain about their financial commitments, prompting them to interact with these deceptive emails. The authenticity of these emails can be hard to discern, making it even more dangerous.
Example Image: Fake Invoice Email
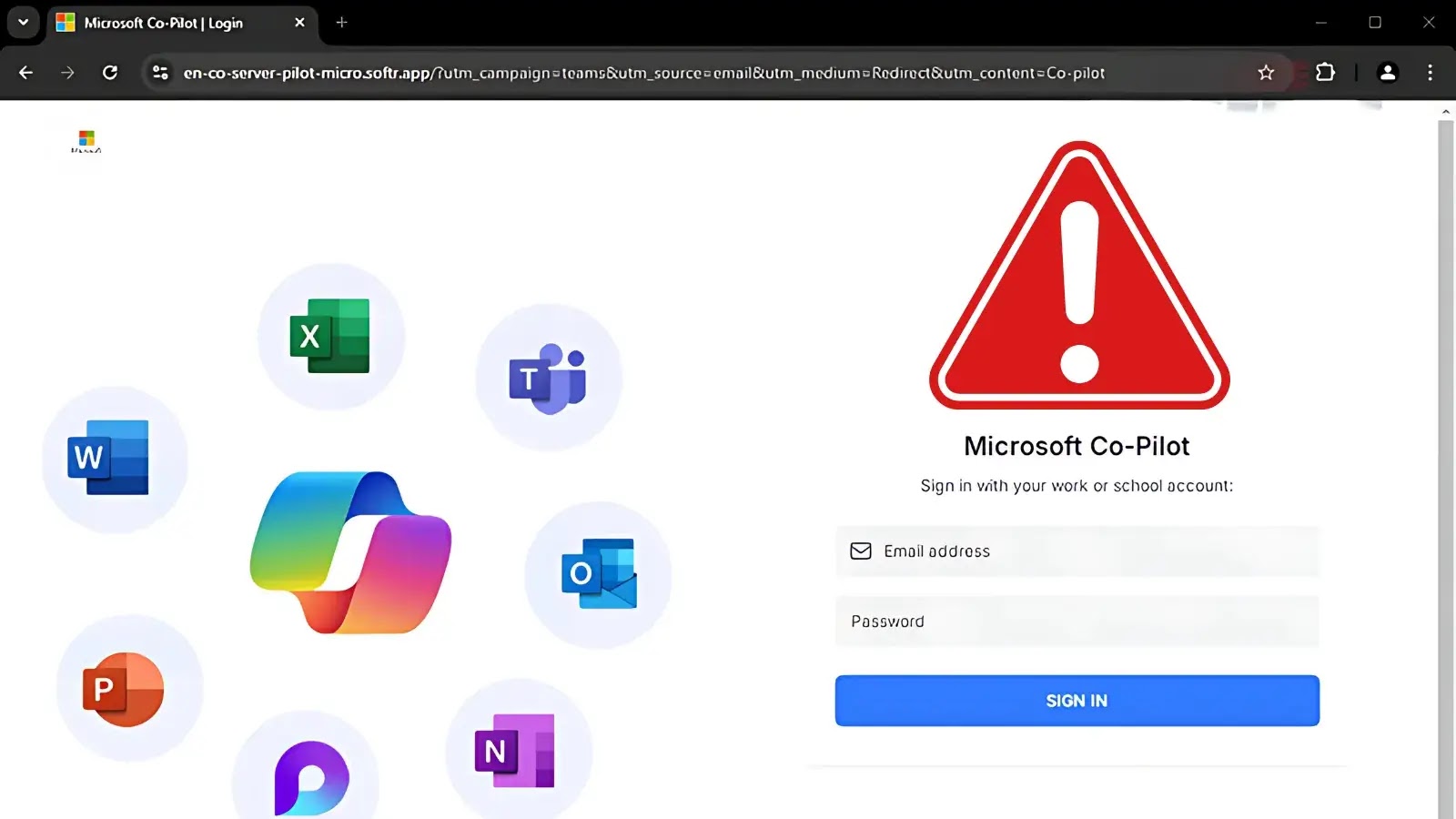
2. Fake Sign-in Pages
- Tactic: If an employee clicks a link in the phishing email, they may be led to a fake login page that imitates the official sign-in for Microsoft Copilot.
- Risk: Users often believe they are entering a secure payment dashboard. However, if they look at the URL, they will find it is not a legitimate Microsoft domain, often featuring suspicious extensions.
Example Image: Phishing Sign-in Page
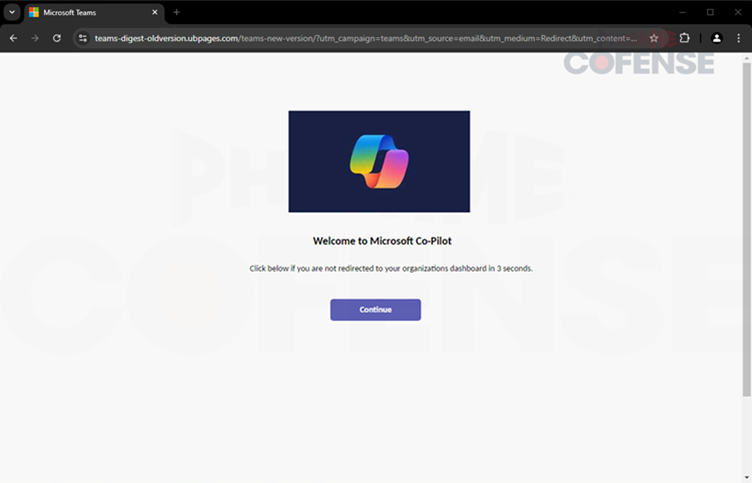
3. Credential Harvesting
- Tactic: The fraudulent site will ask for users’ login details, employing Microsoft branding to make the page look authentic.
- Risk: A noticeable red flag for users is the absence of a password recovery option, indicating that the scammers are just fishing for credentials without offering genuine security features like password resets.
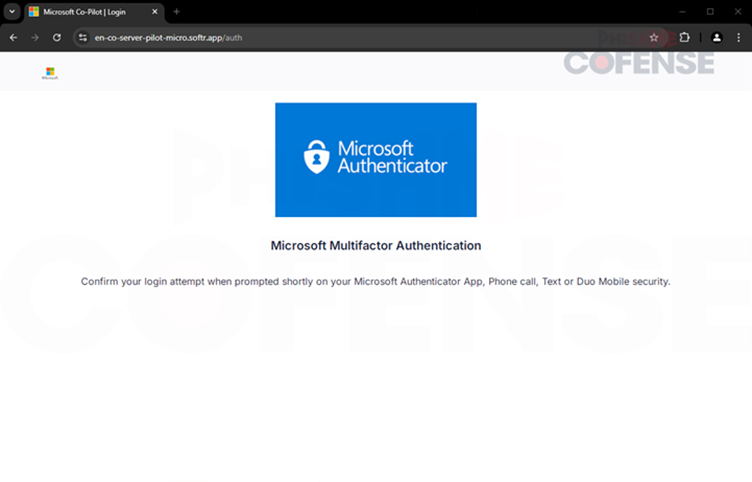
4. Multi-factor Authentication Spoofing
- Tactic: After entering their credentials, users may find themselves redirected to a fake multi-factor authentication page.
- Risk: This technique is designed to buy time for the cybercriminals, as they may exploit the stolen credentials before the victim even realizes the breach.
Example Image: Fake Authentication Page
How to Stay Safe
To defend against these risks, it is crucial for organizations to encourage employee awareness about the proper use of new tools like Microsoft Copilot. Here are several steps that can be implemented:
- Education: Inform employees about legitimate services and costs associated with using Microsoft Copilot.
- Visual Examples: IT departments should provide clear examples of authentic communications so employees can better identify phishing attempts.
- Regular Updates: Keep employees updated on how to recognize potential scams, especially in the context of newly introduced technologies.
The Need for Awareness
As companies increasingly adopt advanced technologies, safeguarding sensitive information must remain a core priority. The exploitation of Microsoft Copilot by hackers clearly illustrates the need for heightened employee awareness and cybersecurity training. By understanding the risks linked to new tools and staying vigilant, employees can significantly reduce the likelihood of becoming victims of sophisticated phishing schemes. As digital landscapes continue to evolve with the integration of AI, training and awareness will be essential in maintaining security.